I had a requirement to use PyCrypto and was running Python 3.6.2. In summary it won't work. If you want to continue with Python 3.6.2, you need to use PyCryptodome.
Otherwise, downgrade to Python 3.5.2 with the follow requirements:
1. Before installation of pycrypto (pip install pycrypto) make sure that you install Microsoft Visual C++ Build Tools (2015)
2. After installation of pycrypto Navigate to Python installation folder (in my case its C:\Program Files (x86)\Python35-32\)
3. Find and edit the script C:\Program Files (x86)\Python35-32\Lib\site-packages\Crypto\Random\OSRNG\nt.py
4. Replace the line (import winrandom) with (from . import winrandom)
Monday, December 18, 2017
Python Script to Read XML Files
Typical use of this when you have M2M interaction and you receive data in XML format where the receiver should react accordingly.
Here is a sample XML file:
************************
Python Code
************************
def get_client_settings (element):
# This function gets client details from XML file
ip_attrib = element.get('ip')
username_attrib = element.get('username')
password_attrib = element.get('password')
email_attrib = element.get ('mail')
for alert in element.findall('alert'):
if alert.get('type').lower() == 'memory':
mem_alert = float(alert.get('limit').replace('%',''))
if alert.get('type').lower() == 'cpu':
cpu_alert = float(alert.get('limit').replace('%',''))
return (ip_attrib, username_attrib, password_attrib, email_attrib, mem_alert, cpu_alert)
for element in root_element.findall('client'):
print ('\nGetting user details')
ip, username, password, email, mem_limit, cpu_limit = get_client_settings (element)
Here is a sample XML file:
************************
Python Code
************************
def get_client_settings (element):
# This function gets client details from XML file
ip_attrib = element.get('ip')
username_attrib = element.get('username')
password_attrib = element.get('password')
email_attrib = element.get ('mail')
for alert in element.findall('alert'):
if alert.get('type').lower() == 'memory':
mem_alert = float(alert.get('limit').replace('%',''))
if alert.get('type').lower() == 'cpu':
cpu_alert = float(alert.get('limit').replace('%',''))
return (ip_attrib, username_attrib, password_attrib, email_attrib, mem_alert, cpu_alert)
for element in root_element.findall('client'):
print ('\nGetting user details')
ip, username, password, email, mem_limit, cpu_limit = get_client_settings (element)
Wednesday, December 6, 2017
ISE Authorization Methods - Basic
- ISE authorization rules processing order
- Takes place only after successful authentication
- Match condition (identity store type, profiling, etc)
- Assign authorization profile
- By default scans sequentially but can be changed to Multiple Matched Rules applied
- Typical use case when you create rule per role (e.g. AD_DACL, NETWORK_DACL, SERVERS_DACL, etc)
- In this case, network engineer can get AD_DACL and NETWORK_DACL
- Another option is to configure one DACL for network users, another DACL for server users, etc
- Its independent from authentication type (MAB, Dot1x or CWA)
- Authorization options
- VLAN Assignment
- You can assign Data VLAN and/or allow Voice VLAN access
- Data VLAN
- It will override the locally configured VLAN on the switch port
- VLAN is provided to NAD using VSA Tunnel-Private-Group-ID
- If no dVLAN is configured, static switchport vlan will be used
- Voice VLAN
- It will grant IP Phones access to connect to the network using the configured voice vlan (no new vlan assignment)
- You need to enable 'Voice Domain Permission' under the authorization policy
- ISE will include the VSA 'cisco-av-pair: device-traffic-class=voice' in ACCESS-ACCEPT to indicate that this is the voice vlan
- ACL
- dACL
- This is Cisco proprietary because it uses Cisco-specific Radius attributes
- ACL is configured in ISE and pushed to the switch
- Filter-ID ACL
- This is IETF standard
- The ACL is configured on the switch
- ISE will provide the switch with ACL name to be applied to the port
- Per-User ACL
- This is Cisco proprietary
- ACL can be configured on ISE and pushed to the switch
- ACL can be configured on the switch and ISE will provide the name to the switch
- IP Address
- ISE can provide IP address to endpoints part of the authorization process using VSA Framed-IP
- Similarly, ISE can provide session time to NAD using Session-Timeout
- Navigate to Administration > System > Deployment > General Settings > Policy Service > Enable Session Services for ISE to handle access-requests and perform authentication/authorization
How ISE Profiling Works?
- ISE Profiling is the service used to identify the type of endpoints connected to the network
- ISE Profiling service should be enabled to probe for endpoint attributes
- The attributes requested are depending on the type of probes enabled (for example dhcp probe will request for dhcp-class-identifier, http probe will request for user-agent, etc)
- Attributes gathered from probes are matched against profiling policies
- Profiling policy is made of set of rules
- Each rule matches a condition and assign certainty factor (CF)
- Certainty Factor (CF) is a weight defines how relevant this condition to decide the final endpoint profile
- The SUM of matched CFs should be greater than or equal to minimum CF configured in the Profiling Policy to profile the endpoint
- In case the endpoint matches more than one profiling policy, the highest CF_SUM decides the final endpoint profile
- Once Profiling Policy is matched , it can trigger exception or execute NMAP scan
- This kicks in ONLY after matching the profiling policy
- Profiling policies can be nested using Parent/Child structure
- Child Profiling Policy won't be matched unless Parent Policy is matched
- Nested Policies are used to granular profiling
- Endpoint will be profiled based on the deepest profile matched in the structure
- Common practice to trigger NMAP scan on Parent Policy to get more attributes for Child policy matching
- Each Profiling Policy can be configured to create Endpoint Identity Group and assign matched endpoints to it.
- You can group Profiles in Logical profiles
- Logical Profiles are containers where you add different profiled devices to provide them one treatment (for example same authorization policies)
- Authorization policies can call Logical Profiles or Endpoint Identity Groups to grant access
- Profiling isn't supported for VPN endpoints due to lack of endpoint MAC address information from VPN Gateway
Change of Authorization
- Radius Change of Authorization (CoA) Access-Request was introduced in order for ISE to issue new authorization policy to the endpoint based CoA triggers
- Endpoint authenticated
- Initial Authorization Policy pushed to the switch (endpoint not yet profiled)
- Profiling data received and endpoint profile selected
- ISE triggers CoA for endpoint to reauthenticate (this is subject to configured CoA Type)
- Final Authorization Policy pushed to the switch based the endpoint profile (during reauthentication process)
- The following scenarios trigger CoA
- Endpoint profiling for 1st time
- Endpoint statically assigned to device identity group
- Endpoint removed from ISE database
- Endpoint dynamically change identity group membership
- Manual CoA from Context Visibility > Endpoints > Change Authorization
Enable ISE SSH Access
If you missed enabling SSH access during the initial setup of ISE, you can enable it using console by pasting the command service sshd enable
Thursday, July 13, 2017
How to find Unassigned Media Resource (No MRG)
To look at media
resources and the allocated MRGs, use the sql query
run sql
select mrg.name as mrg,d.name as resource from mediaresourcegroup mrg inner
join mediaresourcegroupmember mgm on mgm.fkmediaresourcegroup=mrg.pkid inner join device d on mgm.fkdevice=d.pkid
To filter specific
site
run sql
select mrg.name as mrg,d.name as resource from mediaresourcegroup mrg inner
join mediaresourcegroupmember mgm on mgm.fkmediaresourcegroup=mrg.pkid inner join device d on mgm.fkdevice=d.pkid
where d.name like '%AD1%' or mrg.name like '%A01%'
Use this CLI command to find media resources in the default MRG (no assigned to any created MRG).
admin:run
sql select d.name as resource from device as d full outer join
mediaresourcegroupmember as mgm on mgm.fkdevice=d.pkid where and mgm.pkid is NULL
resource
===========
AD1MTP-G711
AD1XCODER
You look for specific device type such as MTP
admin:run
sql select d.name as resource from device as d full outer join
mediaresourcegroupmember as mgm on mgm.fkdevice=d.pkid where d.name like
'%MTP%' and mgm.pkid is NULL
resource
===========
AD1MTP-G711
Subscribe to:
Comments (Atom)
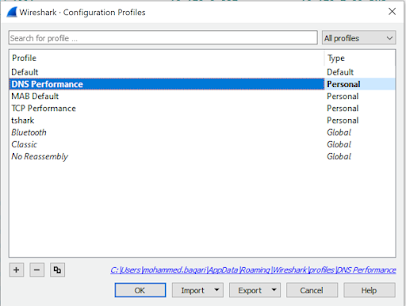
DNS Performance Troubleshooting
When you are troubleshooting internet performance, there are different parts of the connection should be verified: · DNS Pe...
-
From FMC CLI, verify ISE integration status using the command root@vFPMC:/etc/rc.d# cat /var/sf/run/adi-health $status = { 'ADI...
-
If you missed enabling SSH access during the initial setup of ISE, you can enable it using console by pasting the command service sshd ena...
-
Here we will show the configuration of SCEP Enrollment methods (manual enrollment doesn't require any configuration at VPN server si...

